Whitepapers Library |
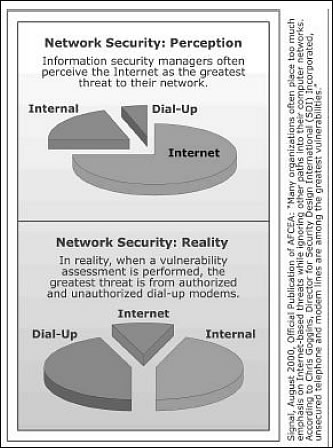
Enterprise Telecom Security ThreatsExecutive SummaryCorporations are typically connected to two public, untrusted networks: the Public Switched Telephone Network (PSTN); and Wide Area Networks (WANs) or the Internet. Traditional phone stations or peripherals connect to the PSTN to enable voice calls, modem and fax communications, and video teleconferencing. Corporate computers connect to WANs or the Internet for data communications and access to information. Internet Protocol (IP) phones and soft phones either connect to the PSTN via a media gateway, or cross the corporate perimeter to connect to WANs or the Internet. Although nearly all corporations secure the Internet connection to their internal data networks with IP firewalls and related technologies, most corporations have yet to lock down their voice connection to the untrusted PSTN, or when present, bring an equal level of security to their IP telephony onnections. An array of vulnerabilities in internal data networks, the traditional phone environment, and other critical corporate infrastructure are accessible through an enterprises unsecured traditional phone network. Although attacks against an enterprises Internet connection receive the most public attention, attacks against an enterprise through the traditional voice network are common. In a data network attack perpetrated through the traditional phone network, intruders bypass Internet-related defenses by using the PSTN to access unauthorized and poorly secured modems. Attackers exploit modems as interconnection devices between enterprise voice and data networks that enable cross-network attacks.
|
Download Information |